The US National Security Agency (NSA) has been indirectly blamed for planting spyware in hard disks built by some of the world's largest manufacturers. The tweaked firmware would give the agency a means to spy on computers all around the globe with the "ultimate persistence and invisibility," according to Kaspersky Labs, a Moscow-based cyber security company.

The Russian researchers and former cyber espionage operatives are reported to have found software hidden deep in hard drives manufactured by Western Digital, Seagate, Toshiba and others, in PCs that were used in 30 countries including Iran, Pakistan, Russia, Syria and China. The countries targeted have been priorities for US intelligence agency attention for many years and targets included government and military institutions, telecommunication companies, banks, energy companies, nuclear researchers, media, and Islamic activists, Kaspersky said. However, the firm declined to directly accuse the US government or its agencies as behind the spying campaign.
The spying operation is said to be just one of a cluster of different spying programs found by Kaspersky Labs, which suggested that that the campaign had "solid links" to the creators of Stuxnet. Stuxnet was the NSA-led cyberweapon which was used to attack a nuclear plant in Iran.
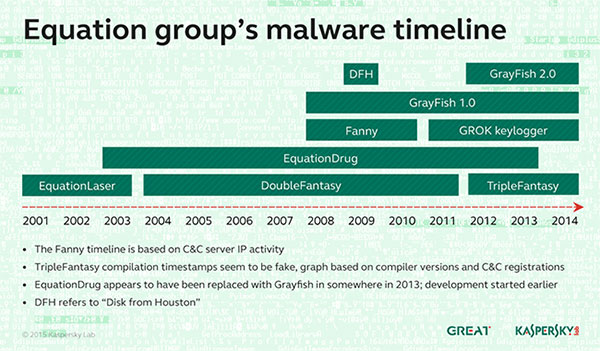
Kaspersky is calling the group of spying programs 'The Equation Group', adding that it is "a threat actor that surpasses anything known in terms of complexity and sophistication of techniques, and that has been active for almost two decades."
The advanced hacking operation was described as "as astonishing technical accomplishment" by the Russian researchers as the spies figured out how to lodge malicious software in the hard disk firmware, which launches every time a computer is turned on and is able to infect the device over and over. This would have given the leaders of the campaign the ability to eavesdrop selectively, steal files, and even establish full remote control over machines.
"To put it simply: for most hard drives there are functions to write into the hardware firmware area, but there are no functions to read it back," said Costin Raiu, director of the global research and analysis team at Kaspersky Labs, reports the FT. "It means that we are practically blind, and cannot detect hard drives that have been infected by this malware."
The NSA would have a number of ways in which it could obtain the drivers' source code required to embed the spyware. These methods include posing as third party software companies or asking for the source directly by requesting it in a security audit from OEMs who wish to sell hard drives to the US Department of Defense, and in turn, use it to infect the manufacturer's shipping products.
Western Digital, Seagate and Micron said they had no knowledge of these spying programs. Toshiba, Samsung and IBM have either declined to comment or haven't got back to the FT concerning the firmware spyware programs.













