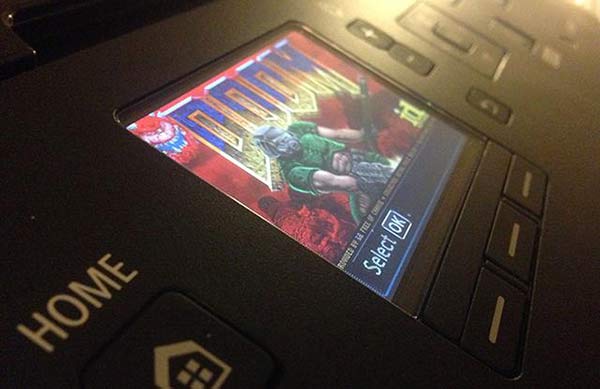
Net connected appliances might offer greater user convenience but they are also exposed to remote hacking. This kind of problem is only going to get bigger with the impending wave of devices which will form the Internet of Things (IoT). The remote hacking of a Canon Pixma printer to play Doom on its diminutive colour preview display demonstrates device security vulnerability in a most nerd-attention grabbing fashion.
In an impressive demonstration of how thoroughly net connected devices can be hacked Michael Jordon, from Context Information Security, compromised a Canon Pixma printer and ran Doom upon it. This was the centrepiece of his talk at the 44Con ethical hacker conference in London.
Mr Jordon found that the Canon Pixma printer he used can be accessed via the internet using a web interface to check on queued jobs, device status and so on. The interface has no user name or password and is open to discovery. While this kind of info might not be particularly sensitive Jordon found that the printer firmware was also updatable via this web interface. He reverse engineered the encrypted firmware to reveal the computer code and thus discovered how to replace it with his own firmware which would in turn be accepted as authentic.
The above procedure opened up the printer to all sorts of dodgy hacks, as you could imagine. However, as an ethical hacker, Jordon just wanted to highlight the potential problems in connected devices like the Canon Pixma. "Running Doom, that's real proof you control the thing," he told the BBC.

The hacked Canon Pixma has a "32-bit Arm processor, 10 meg of memory and even the screen is the right size," explained Jordon. He took several months of his spare time to get Doom to run but other than a slightly off colour palette "it runs quite quickly, though it's not optimised," he reflected. He won't be spending more time to fine tune the game as he's "done" with the project.
Canon has responded to Mr Jordon's hack by saying it will fix the vulnerabilities as soon as it can. All new Pixmas and models launched from Q2 2013 will be updated to request a user/pass to make use of the web interface. Earlier models are not affected.
You can read further details about Jordon's hack on the Context blog.













