FileZilla is a very popular fully featured open source FTP client which has been the target of malware writers before but a new campaign, backed by many third party websites, is the largest ever seen to date, reports PC Advisor.
The FileZilla blog says that this threat to would-be FileZilla downloaders is being addressed as best as it can and it is "taking measures to get the known offenders removed." For FileZilla it's not so simple to track down and prevent tainted versions of the software because, as part of the free open source software and the GNU General Public License, (beneficial) redistribution and modifications are encouraged.
If perhaps you haven't paid much attention to where you downloaded your copy of FileZilla you might be getting more than you bargained for with this malware infested version. Security software company Avast says that the iffy FileZilla versions are as up-to-date as the official versions (up to 3.7.3 right now) but that these programs will seek to steal your FTP login credentials bypassing your firewall as it is part of the main program; "The whole operation is very quick and quiet." Other than that the FTP client is fully functional and operates as you would expect.
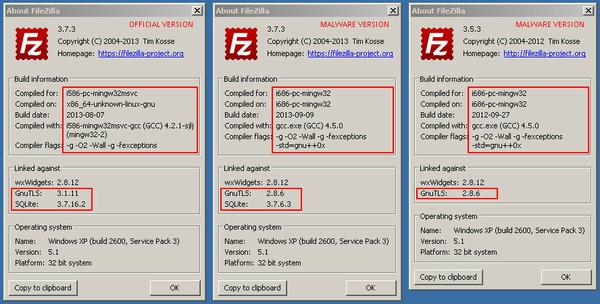
A quick check to see if the FileZilla FTP program on your computer is a tainted version is possible via the about box; the use of older GnuTLS/SQLite versions as can be seen in the screenshots below. Also you will find the malware infected version will not update; which for versions 3.7.3 is logical at this time as it's the newest release. However it still won't update when a newer version comes out, in order to protect itself from replacement.
click to zoom image
What would happen to your FTP login data if you used this hacked version of the program? The Avast blog reveals that stolen data would be sent to individuals or organisations using the "infamous Russian domain registrar Naunet.ru, which is associated with malware and spam activities". This registrar doesn't display client contact info or respond to suspension requests. It is assumed that the FTPs will then be used for further spread of malware and if your site uses a payment system that is also vulnerable.
It is recommended that users always download FileZilla directly from the official FileZilla website or the SourceForge page.