Tokyo's National Institute of Information and Communications Technology (NICT) officials said on Monday that a record 12.8 billion cyberattacks were detected by the nation's agencies in 2013, largely targeting government organisations and other state-run activities.
NCIT officials said that the number was the highest since the institute started cyberattack surveys back in 2005 and includes phishing campaigns, DDoS (Distributed Denial of Serice) attacks, and Hacktivism. "Cyber-attacks from emerging countries, as well as China and the United States, have been increasing," an NICT official stated.

Even though there are no exact figures for the number of attacks originating from each country, it was believed that most of the attacks originated from China and the US, and those from Russia, Brazil as well as locations in Japan also increasing.
A system has been developed which uses around 210,000 sensors to determine whether access to servers of state-run organisations are of the malicious cyberattack variety. The number of cyberattacks detected by NICT through its sensors increased from around 300 million in 2005, to 5.7 billion in 2010 and around 7.8 billion in 2012, partly due to gradual increase in the number of sensors installed for such detection. Whilst the number of cyberattacks expanded 1.6 times in 2013 from 2012, the number of sensors also increased 1.1 times.
According to the report by Japan's Kyodo News agency, attacks on government servers noticeably increased after international hacker group Anonymous criticised Japan's whaling activities last May.
DDoS Attack Hits 400Gbit/s
In related malicious hacking news, a record-breaking DDoS attack on Monday peaked at 400Gbit/s, which is around 100Gbit/s more than the largest previously seen attacks including last year's Spamhaus incident.
Matthew Prince, CEO on anti-DDoS protection outfit CloudFlare tweeted the following:

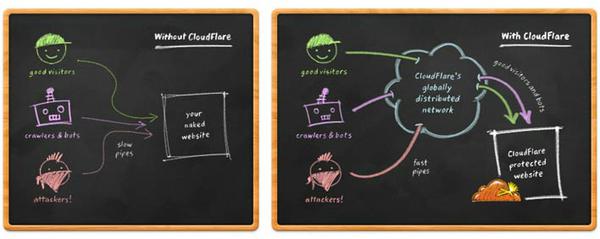
Although the company did not reveal which of its customers was targeted, the attack was so large that it affected CloudFlare's entire global network.
The attack to flood the European servers with data was launched by leveraging weaknesses in the Network Time Protocol (NTP), used to synchronise computer clocks. The trend of launching DDoS attacks using NTP has only recently become popular, although researchers have long-predicted these possibilities.
The process involves sending requests with spoofed source IP addresses to NTP servers with the purpose of making those servers return responses to the spoofed addresses as a substitute for the real senders. "Someone's got a big, new cannon. Start of ugly things to come," Tweeted CloudFlare's Prince on Monday.