Since March 2010 Iran has been targeted by a data monitoring and collecting piece of malware now known as Flame. Analysts say the malware is so complex in nature that they believe it could only have been developed by a government agency or state with a very big budget. The purpose of the Flame malware is to gather data and send it to its command and control servers of which there are approximately 80 known to exist.
Crysys Lab, a special unit that investigates computer viruses at Budapest University said of Flame “It covers all major possibilities to gather intelligence, including keyboard, screen, microphone, storage devices, network, Wi Fi, Bluetooth, USB and system processes. Information gathering from a large network of infected computers was never crafted as carefully”.
The “Worm.Win32.Flame” malware infects Windows based computers and weighs in at a rather large 20MB. Unlike single-shot predecessors Stuxnet and Duqu Flame is a complete attack toolkit that can steal data from many different sources. For example rather than just recording VoIP calls the program can turn on the computer microphone and begin recordings at will, while simultaneously taking screenshots of interesting apps (usually instant messaging apps).
The main features of the virus as listed by the Iran Maher CERTCC are:
- Distribution via removable medias
- Distribution through local networks
- Network sniffing, detecting network resources and collecting lists of vulnerable passwords
- Scanning the disk of infected system looking for specific extensions and contents
- Creating series of user’s screen captures when some specific processes or windows are active
- Using the infected system’s attached microphone to record the environment sounds
- Transferring saved data to control servers
- Using more than 10 domains as C&C servers
- Establishment of secure connection with C&C servers through SSH and HTTPS protocols
- Bypassing tens of known antiviruses, anti malware and other security software
- Capable of infecting Windows XP, Vista and 7 operating systems
- Infecting large scale local networks
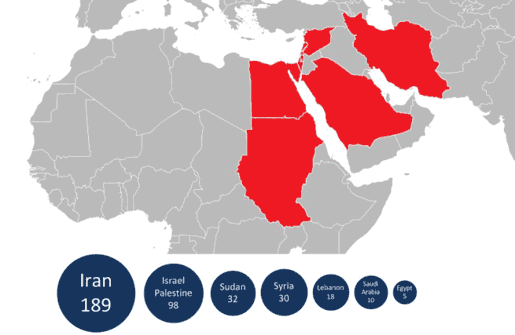
Flame infections detected by Kaspersky Lab
Experts believe the Flame espionage virus spread itself via phishing, website download or USB pen drives and perhaps further unidentified methods. The complexity of the virus is such that researchers are only just beginning to see how it works and what it does. Kaspersky Labs Alexander Gostev told Wired. “It took us half-a-year to analyze Stuxnet. This is 20-times more complicated. It will take us 10 years to fully understand everything.” On trying to pin down exactly how to classify Flame the Kaspersky Lab expert said “It is a backdoor, a Trojan, and it has worm-like features, allowing it to replicate in a local network and on removable media if it is commanded so by its master.”
In a Kaspersky blog update today the company confirmed Flame is the same virus as SkyWiper detailed by Crysys Lab and Flamer as found by the Iran Maher Cert Group. This very large and complex malware has been mining data for over 2 years specifically targeting Iran. High profile organisations in Iran received software capable of neutralising Flame in early May. Some experts believe the Flame espionage virus is related to the Stuxnet virus and was created by a USA or Israel based agency.













