We've been told on multiple occasions that GPGPU computing is the future and that the massive parallelism of graphics-cards can speed up a huge number of tasks. However, researchers have now come up with a slightly more malicious use for all of that processing power - GPU-assisted malware.
The team from Greece and the US has developed proof of concept code that offloads some of the components of the malware to the GPU, making it very difficult to detect.
The first technique uses the GPU to unpack the malicious code. ‘Packing' is commonly used to hide viral code by compressing or encrypting it before being automatically unpacked at runtime. The specific algorithm can also be changed on a regular basis, making detection even harder. Using the raw-power of a GPU, more complex encryption schemes can be used to obscure code that wouldn't be feasible on a CPU.
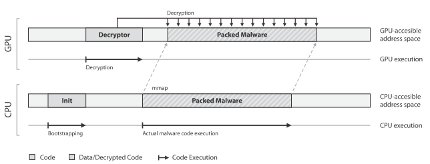
As well as the more intricate scheme, the majority of the code would be written for the GPU, leaving a very small footprint of x86 code in system memory. Since current virus detection software is designed mainly or exclusively to monitor this sort of software, detection becomes even less likely.
The research team also showed how GPUs could be used to enhance run-time polymorphism. This technique decrypts only a small part of the necessary code at a time, preventing the complete virus from being exposed - and vulnerable to detection - at once. Not only will a graphics-card be able to decode and re-encode segments of the virus more quickly, but by storing all of the decryption instructions exclusively in the graphics memory, control is constantly switching between CPU and GPU. This makes the process of reverse engineering and analysis very difficult.
For those interested in further details, the full paper - which is surprisingly accessible, even to those without a background in computer science - is available to read in PDF format here.













