Many HEXUS readers may own, run, or maintain Wordpress based websites, as it is one of the most popular web publishing platforms / CMS available. It is quite common to have an SEO plugin to help optimize certain aspects of your site structure, pages and posts for Google etc, but one such plugin was recently discovered to leave sites highly vulnerable due to an XSS vulnerability.

Wordpress plugins are numerous and flaws quite commonplace, but I thought this particular flaw was worth highlighting as it has 100,000+ users and the flaw appears to have been particularly nasty. ThreatPost reports that "the bug would allow a number of malicious actions, up to and including full site takeover".
In its more technical analysis of the SEOPress plugin's issues, the WordFence security plugin blog says that the flaw in SEOPress allowed "an attacker to inject arbitrary web scripts on a vulnerable site". It appears to be the case that the scripts would execute anytime a legitimate user or admin visited the 'All Posts' section of the Wordpress CMS.
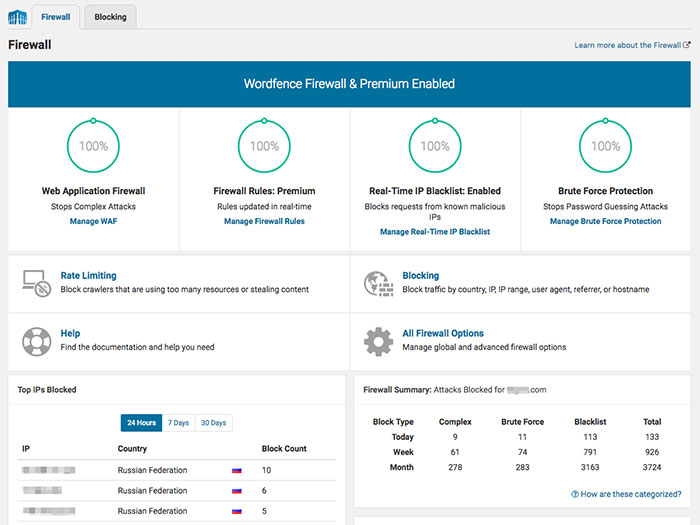
At the time of writing, the WordFence security plugin protects against the SEOPress flaw mentioned above, using a Firewall rule for Premium users. WordFence Premium users have got the firewall rule auto-applied, free version users would also have been alerted. From 28th August, the same firewall protection is going to be put in place for WordFence free users. Perhaps more importantly, SEOPress version 5.0.4, made available on 4th August by the developer, eradicates the flaw for anyone who updates.
Of course, if you look after any Wordpress installs you should check to see if you have the SEOPress plugin installed, and if so update it immediately. Lastly, if it is installed but not activated, perhaps from a time you might have given it a test run, you should probably uninstall it. Let Wordpress admin friends know about this flaw too, in case they haven't have visited admin pages and updated plugins for a while.














