Yesterday it emerged that classified US-UK trade documents that leaked out ahead of the 2019 general election were stolen from the email account of former trade minister Liam Fox by suspected Russian hackers. Reuters reported that it had two sources with direct knowledge of the matter, speaking on condition of anonymity. UK authorities are now investigating the hack, as a "criminal investigation," thought to be the result of a Russian state-backed campaign.

According to the Reuters report, the sensitive trade documents were purloined between 12th July and 21st October last year as the hackers managed to access Fox's email account "multiple times" between those dates.
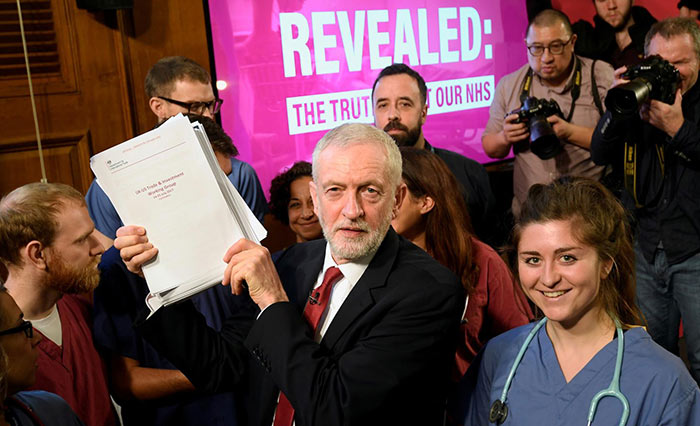
The stolen classified documents were posted online by an anonymous internet user in the run up to the general election and Labour, the main opposition party, sought to highlight their content as evidence that the NHS was on the negotiating table in a US-UK trade deal. The Conservatives had very vocally denied the NHS was 'up for sale' in any way to US health corporations and there was a lot of debate about this ahead of the vote.
Ahead of the highly anticipated Russia Report, British foreign minister Dominic Raab said that 'Russian actors' had sought to interfere in the 2019 general election "through the online amplification of illicitly acquired and leaked Government documents". Perhaps he was trying to make the first move in a kind of 'both sides' argument with regard to foreign influence of British democratic processes ahead of the Russia Report.
So, how did the Russian state backed hackers get hold of the documents in question? It didn't require any sophisticated malware, self-replicating tunnelling cyber-IP worms, or some such mythical black-hat networking technologies. Fox was simply duped by a spear phishing email and handed over his account login details.
Tim Sadler, Tessian CEO, released a statement about the attack today. He noted that attackers "tricked Mr Fox into sharing his account login details so that they could access his account, multiple times over the space of many months, in order to steal politically sensitive and classified documents". Sadler observes that spear phishing is a lucrative and relatively simple attack method with a high ROI.
As the US election time nears Sadler says that this news is an important warning for security teams in government organisations. Steps need to be in place to detect impersonation scams which make spear phishing a useful attack vector.













