Microsoft has published a security advisory about a zero-day vulnerability affecting its Windows OS. The software giant says it is aware of a number of targeted attacks which could "leverage un-patched vulnerabilities in the Adobe Type Manager Library" (atmfd.dll). These are worrying remote code execution (RCE) vulnerabilities which could be exploited using a specially-crafted multi-master font - in Adobe Type 1 PostScript format.
Apparently all an attacker needs to do is get you to open a specially crafter document with the font embedded or view it in the Windows preview pane - to trigger the exploit (but the Outlook preview pane is safe). Once exploited the attacker could run code on the user's system. Some attacks in the wild have been observed though Microsoft says they are so far limited and targeted.
All currently supported versions of Windows and Windows Server are affected by the vulnerability. Notably Windows 7 users are susceptible too, but that OS is beyond its end-of-support date. Microsoft says Windows 7, Windows Server 2008, or Windows Server 2008 R2 will need an ESU license to get patched.
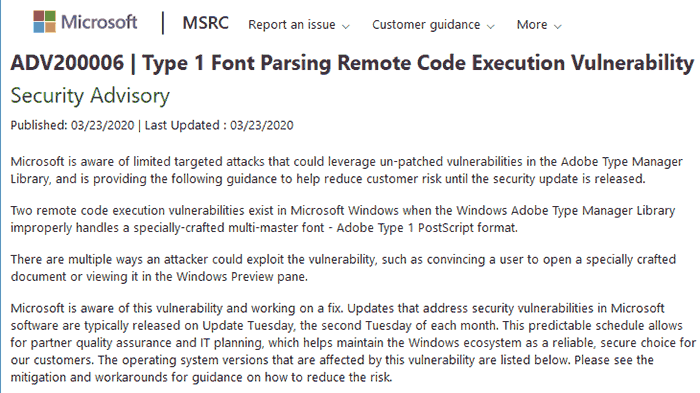
In ADV200006, Microsoft says it is working on a fix for the atmfd.dll vulnerability. It hints that it will be patched during the next patch Tuesday set of fixes, as it has decided not to patch this out of step with that schedule (2nd Tuesday of each month - next available date is Thurs 14th April).
In the meantime, Windows users can implement various workarounds, as detailed by Microsoft. The workarounds are pretty straight forward, varying from disabling the Windows preview pane, or disabling the WebClient service, to renaming atmfd.dll so it isn't used by the system. However, some workarounds mean that OTF fonts won't preview in Windows, or won't even work in any Windows applications at all.













