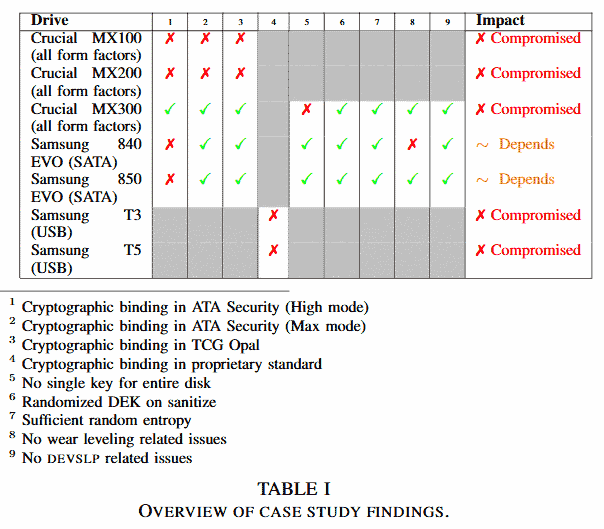
In the wake of the "pattern of critical issues" in SSD encryption, revealed last year by researchers at Radboud University in Holland, Microsoft issued a security advisory regarding a vulnerability that affects hardware-based encryption on SSDs. The issue was because of SSD firmware makers using master passwords and / or faulty standards implementations - thus your hardware encrypted data would be pretty easy to poke through in many cases.
Initially Microsoft recommended admins configure BitLocker to "enforce software encryption," in light of the vulnerabilities in the hardware encryption of certain self-encrypting drives (SEDs). Now it has gone a step further, with an update to Windows 10 default BitLocker behaviour - meaning the system will by default use software encryption - even if the drive is flagged as 'self-encrypting'.
Within the Windows 10 1709 update KB4516071 released last week you will find there are numerous improvements and fixes. As well as the highlighted update to an issue that "causes excessive CPU usage when you switch applications or hover over the Taskbar," Microsoft listed a change that affects BitLocker encryption. The full entry on this aspect of the update reads as follows:
"Changes the default setting for BitLocker when encrypting a self-encrypting hard drive. Now, the default is to use software encryption for newly encrypted drives. For existing drives, the type of encryption will not change."
Many SSD makers boast about their on-the-fly encryption and in theory it should work better and more efficiently using a dedicated on-device encryption processor to take this task away from your Windows PC's CPU. However, if your security isn't secure its completely pointless, a waste of time and resources, and gives you a false sense of security.
Thankfully, if you do own drive(s) with strong security - and it works as advertised - you can still toggle Bitlocker to trust the built-in security in those instances. This is just a default change for new users/setups.













